11.6.1.3 explain the purpose of network hardwareNetwork Hardware
How does the workstation connect with the network? Wired and wireless connections
Computers need networking hardware in order to connect to each other. Hub
A hub can also function as a repeater. A repeater extends the reach of a network because it rebuilds the signal, which overcomes the effects of data degradation over distance. The hub can also connect to another networking device, like a switch or router that connects to other sections of the network. Hubs are used less often today because of the effectiveness and low cost of switches. Hubs do not segment network traffic, so they decrease the amount of available bandwidth for all devices connected to them. In addition, because hubs cannot filter data, a lot of unnecessary network traffic constantly moves between all the devices connected to it. Bridge LANs are often divided into sections called segments, similar to the way a company is divided into departments, or a school is divided into classes. The boundaries of segments can be defined using a bridge. A bridge connects two LAN segments and filters network traffic between LAN segments. Bridges keep a record of all the devices on each segment to which the bridge is connected. When the bridge receives a frame, the bridge examines the destination address to determine if the frame is to be sent to a different segment or dropped. The bridge also helps to improve the flow of data by keeping frames confined to only the segment to which the frame belongs. Switch
Switches maintain a switching table. The switching table contains a list of all MAC addresses on the network, and a list of which switch ports can be used to reach a device with a given MAC address. When a frame arrives that is destined for a particular MAC address, the switch uses the switching table to determine which port to use to reach the MAC address. The frame is forwarded from the port to the destination. By sending frames out of only one port to the destination, other ports are not affected. Modem
The modem converts digital data to analog signals for transmission over a phone line because analog signals change gradually and continuously, they can be drawn as waves. In this system, the digital signals are represented as binary bits. The digital signals must be converted to a waveform to travel across telephone lines. They are converted back to bits by the receiving modem so that the receiving computer can process the data.
Routers
Wireless access point Wireless access points provide network access to wireless devices, such as laptops and tablets.
Firewall
Hardware firewalls are different from software firewalls, which are installed on individual computers and provide protection at the software level. Hardware firewalls provide network-wide protection and can be more effective in preventing attacks on your network. Hardware firewalls use a variety of techniques to protect your network, including packet filtering, stateful packet inspection, and application-level gateways. Hardware firewalls are typically more expensive than software firewalls, but they offer a higher level of security and are generally easier to manage. They are commonly used in medium to large-sized organizations where network security is a critical concern. Considerations when selecting a hardware firewall include:
Questions:
Exercises: Ex. 1 Quiz "Network Design" Ex. 2 Game Noughts & Crosses "Computer Networks" Exam questions:
| |||||
|
| |||||
| Просмотров: 8098 | Комментарии: 1 | | |||||
| Всего комментариев: 1 | |
|
| |
 Switches are sometimes called multiport bridges. A switch has several ports, depending on how many network segments are to be linked.
Switches are sometimes called multiport bridges. A switch has several ports, depending on how many network segments are to be linked. 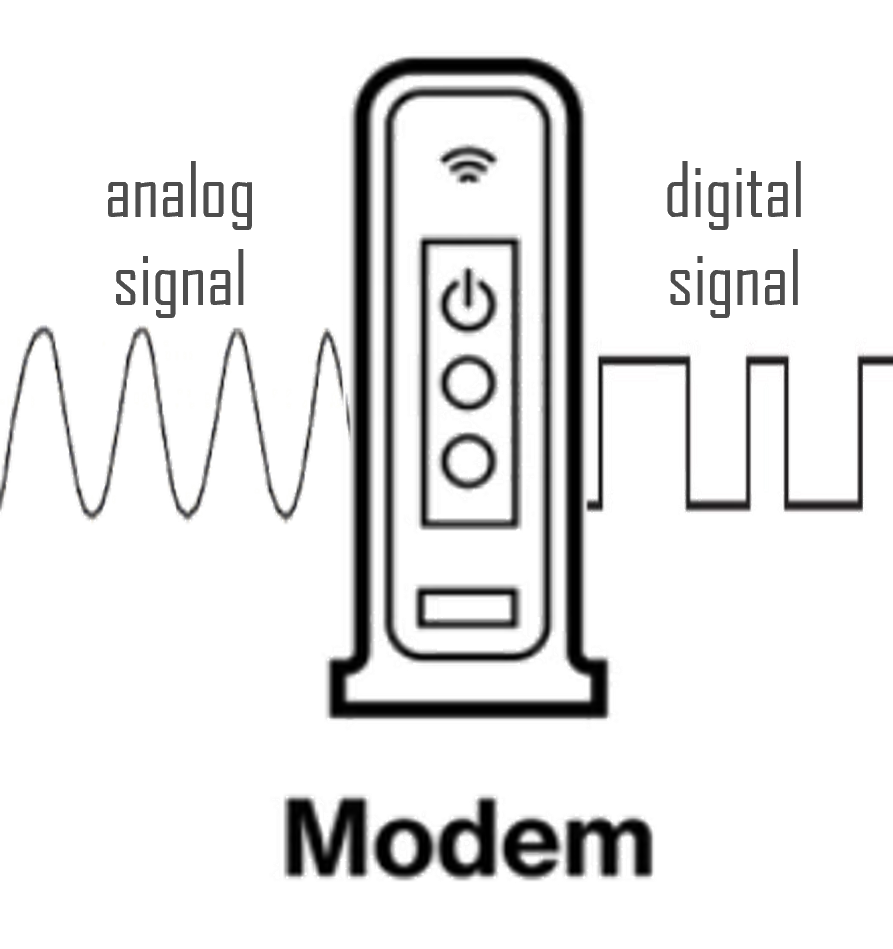 A
A  Routers connect networks to each other. Switches use MAC addresses to forward a frame within a single network. Routers use IP addresses to forward packets to other networks. A router can be a computer with special network software installed or a device built by network equipment manufacturers.
Routers connect networks to each other. Switches use MAC addresses to forward a frame within a single network. Routers use IP addresses to forward packets to other networks. A router can be a computer with special network software installed or a device built by network equipment manufacturers. The wireless access point uses radio waves to communicate with the wireless NIC in the devices and other wireless access points. An access point has a limited range of coverage. Large networks require several access points to provide adequate wireless coverage. A wireless access point provides connectivity only to the network, while a wireless router provides additional features, such as assigning IP addresses.
The wireless access point uses radio waves to communicate with the wireless NIC in the devices and other wireless access points. An access point has a limited range of coverage. Large networks require several access points to provide adequate wireless coverage. A wireless access point provides connectivity only to the network, while a wireless router provides additional features, such as assigning IP addresses. A hardware firewall is a physical device that sits between your computer network and the internet and works by inspecting all incoming and outgoing traffic to determine if it meets certain security criteria.
A hardware firewall is a physical device that sits between your computer network and the internet and works by inspecting all incoming and outgoing traffic to determine if it meets certain security criteria.